Automate content and supercharge processes
Drive end-to-end productivity, collaboration, and compliance with Doxis - your next generation of enterprise content management.

Improve your enterprise
content management
Everything you need to work better, faster and more securely.
Document management
Digitize, understand and work on documents
Learn more →
Team collaboration
Collaborate from anywhere with anyone
Learn more →
Intelligent archive
Securely store and find information
Learn more →
Process automation
Automate business processes and tasks
Learn more →
Content understanding
Extract information and create/generate insights
Learn more →
Connecting business apps
Integrate seamlessly with best-of-breed applications
Learn more →
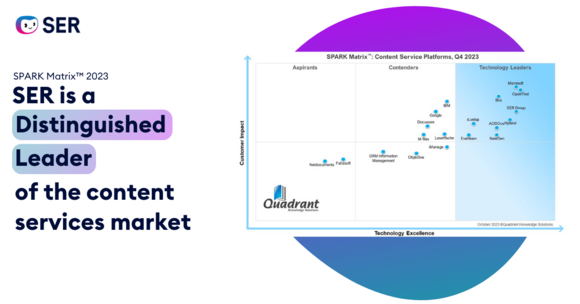
Customers and analysts love SER and Doxis




Tailored solutions for your digital transformation
Faster time-to-value, streamlined manufacturing processes
Leading manufacturing companies optimize all processes related to production through Doxis. The entire purchase-to-pay process is digitized, accelerated and automated - ensuring higher customer satisfaction through the reliable and timely delivery of goods.
- Faster procurement processes
- Improved production planning
- Transparent project management
- Documented QM processes

All documents relevant to production are compiled in one efile where the user can search through them. This makes work so much easier.
Christian Döring
Process Engineering, Neways Electronics Riesa GmbH & Co. KG

Streamlined processes, ensured compliance
Top financial service providers are gaining a competitive advantage through agile banking processes. Doxis helps you to meet customer expectations, speed up response times, reduce costs and automate compliance.
- Better customer service
- Swifter loan processing
- Improved resource utilization
- Mitigated legal risks

Questions such as 'Which loan processes were in place on March 14, 2015?’ can be answered easily and immediately today using our ECM system.
Petra John
Procedures Officer, Aareal Bank Gruppe

Optimized claims processes, shorter response times
Successful insurance providers don’t leave their customers waiting. Doxis helps you to offer first-class customer service and speed up underwriting and claims processes.
- 360° view of policy holders
- Expedited claims processes
- Better customer service
- More efficient use of resources

The customers notice that our processing speed is higher due to the fact that we respond so much faster.
Alexander Erpenbach
Head of the Policy Department for the divisions Property, Liability, Accident, Automotive Insurance and Customer Center Service, DEVK Versicherungen

Information and goods logistics in sync
Billions of documents, tens of thousands of users: Doxis is the ECM platform of choice of the largest logistics corporations in the world. Give customers information at any time about the whereabouts and estimated arrival of their packages through transparent documentation.
- Access documents from everywhere
- 360° view of shipping operations
- Real-time delivery updates for customers
- Audit-proof archiving of billions of shipping documents

Working together is so much easier now in the TGW Group. We continue to grow together as a corporate group, because we have access to the same data and can efficiently share information.
Johannes Gebetsberger
Application Services Project Manager, TGW Logistics Group GmbH

Tailored solutions for your digital transformation
Faster time-to-value, streamlined manufacturing processes
Manufacturing leaders keep their production running smoothly. Doxis enhances efficiency across your production processes - for a higher customer satisfaction due to reliable and on-time delivery of goods.
- Production continuity
- Improved production planning
- Transparent project management
- Documented QM processes
All documents relevant to production are compiled in one efile where the user can search through them. This makes work so much easier.
Christian Döring
Process Engineering, Neways Electronics Riesa GmbH & Co. KG

Streamlined processes, mitigated legal risks
Top financial institutes get ahead of competition with agile banking processes. Doxis helps you to meet customer expectations, speed up response time, reduce costs and automate compliance.
- Better customer service
- Swift loan processing
- Improved resource utilization
- Mitigation of legal risks
Questions such as 'Which loan processes were in place on March 14, 2015?’ can be answered easily and immediately today using our ECM system.
Petra John
Procedures Officer, Aareal Bank Gruppe

Optimized claims processes, shorter response times
Successful insurance providers don’t leave their customers waiting. Doxis helps you to offer first-class customer service and speed up underwriting and claims processes.
- 360° view of policy holders
- Expedited claims processes
- Better customer service
- More efficient use of resources
The customers notice that our processing speed is higher due to the fact that we respond so much faster.
Alexander Erpenbach
Head of the Policy Department for the divisions Property, Liability, Accident, Automotive Insurance and Customer Center Service, DEVK Versicherungen

Excellence in worldwide logistics, high capacity document management
Logistics champions manage billions of documents and tens of thousands of users. Doxis helps you to access documents worldwide and keep your customers fully informed about their shipments
- Access documents from everywhere
- 360° view of shipping operations
- Real time delivery information for customers
- Audit-proof archiving of billions of shipping documents
Working together is so much easier now in the TGW Group. We continue to grow together as a corporate group, because we have access to the same data and can efficiently share information.
Johannes Gebetsberger
Application Services Project Manager, TGW Logistics Group GmbH

More than software – your expert for digital transformation
Consulting and implementation
Enhance the impact of digital transformation
Learn more →
Managed services
Focus on your business, we'll do the rest
Learn more →
SERacademy training
Learn how to maximize the effectiveness of Doxis
Learn more →
SER named a Leader in 2023 IDC MarketScape